- Terms and Conditions
- Disclaimer
- Privacy Policy
eREC Terms of Service
Effective Date: October 1, 2025
Last Updated: October 1, 2025
Welcome to the electronic Record of Emergency Contacts (“eREC”), an online service provided by findeREC Inc. (“Company,” “we,” “us,” or “our”). By accessing or using the eREC website located at www.findeREC.com (the “Website”) and related services (collectively, the “Service”), you agree to be bound by these Terms of Service (the “Agreement”).
If you do not agree, please do not use the Service. If you register as a member or co-member (“Member”), your enrollment confirms acceptance of these Terms.
1. Eligibility
- You must be at least 18 years old to use the Service.
- By registering, you represent that you have the authority and capacity to enter into this Agreement.
- Membership is void where prohibited by law.
2. Membership & Term
- Basic Membership: Free.
- Premium Membership: Paid, valid for one (1) year from enrollment date.
- Membership continues until expiration, cancellation, or termination.
3. Cancellations & Refunds
- Cancellation by Member: You may cancel at any time via your account or in writing to findeREC.
- Cancellation by findeREC: We may suspend or terminate your account if you violate this Agreement. No refund is provided if terminated for breach.
- Refunds: Premium Members may request a full refund within 30 days of initial enrollment by emailing cancellations@findeREC.com.
4. Account Security
- You are responsible for maintaining the confidentiality of your username and password.
- You agree to notify us immediately of any unauthorized access.
- Each account is for individual use and may not be shared without authorization.
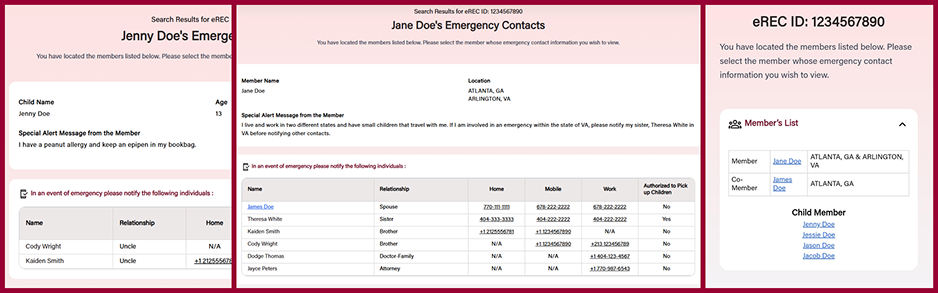
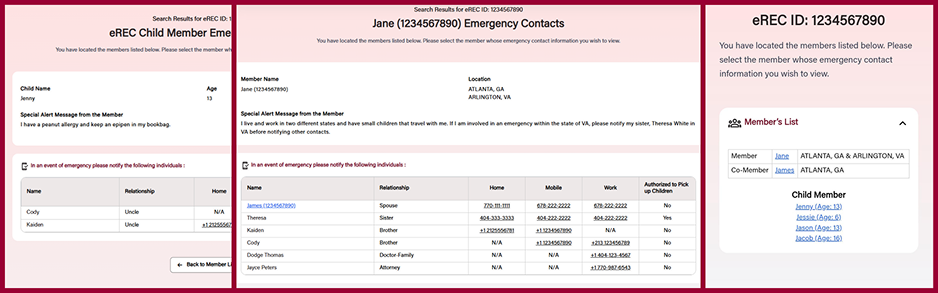
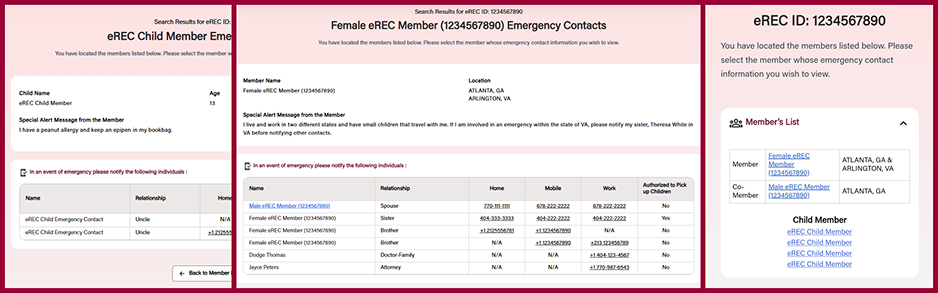
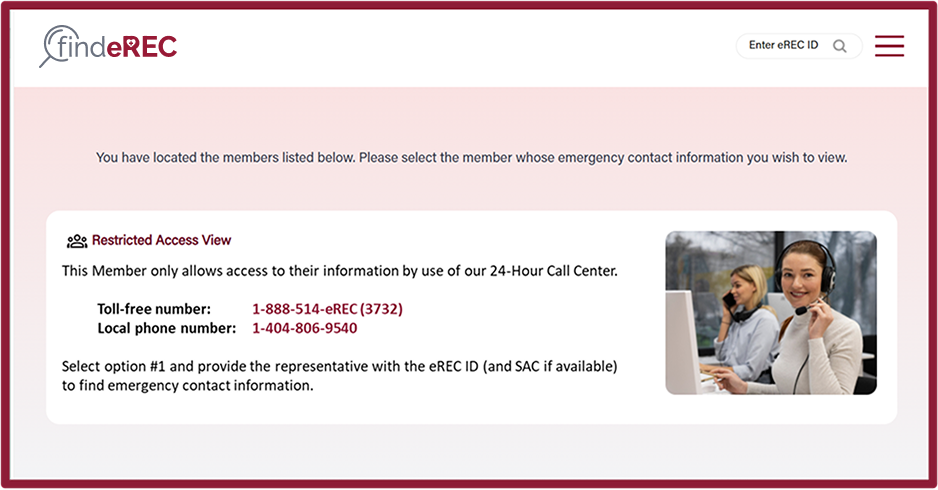
5. eREC ID & Security Access Code
- Upon enrollment, you will receive a unique eREC ID number, which may be displayed on your Member card.
- You may also create a Security Access Code to further restrict access to your emergency contact information. You are responsible for sharing this code with trusted individuals or organizations.
6. Group Membership
- Organizations (e.g., employers, schools) may establish group memberships with discount offers.
- Group IDs allow eREC to identify new Members within a group.
- Groups are not responsible for paying individual membership fees unless explicitly agreed in writing.
7. Member Content & Responsibilities
- You are solely responsible for the information you provide, including emergency contact details.
- You must obtain permission from individuals before listing them as emergency contacts.
- Prohibited content includes but is not limited to:
- Hate speech, threats, or harmful material.
- False, misleading, or illegal content.
- Unauthorized solicitation, spam, or advertising.
- Exploitative or abusive content.
8. Intellectual Property
- findeREC Inc. owns all rights to the Website and Service, including trademarks, logos, and software.
- You may not copy, modify, or distribute our proprietary materials without written consent.
9. Copyright Policy
If you believe your copyrighted material has been used without permission, contact us at:
PO Box 196942, Atlanta, GA 30321
Please include all required DMCA notice elements.
10. Limitation of Liability
- To the fullest extent permitted by law, findeREC Inc. is not liable for indirect, incidental, or consequential damages (including lost profits).
- Our total liability is limited to the amount paid by you for the Service during your current membership term.
11. Indemnification
You agree to indemnify and hold harmless findeREC Inc., its affiliates, and employees from any claims or damages arising out of:
- Your use of the Service,
- Your violation of this Agreement, or
- Your inclusion of third-party information without consent.
12. Disputes & Governing Law
This Agreement is governed by the laws of the State of Georgia, USA. Any disputes will be resolved in the state or federal courts located in Georgia.
13. Entire Agreement
This Agreement constitutes the full understanding between you and findeREC Inc. If any part is found unenforceable, the remaining provisions remain in effect.
eREC Disclaimer
- The Service provides a platform for storing and sharing emergency contact information.
- findeREC Inc. does not verify the accuracy of information provided by Members.
- Members are solely responsible for obtaining consent from individuals listed as emergency contacts.
- findeREC Inc. is not responsible for:
- Locating emergency contacts,
- Technical errors, interruptions, or security breaches,
- The actions or conduct of Members or third parties,
- Loss, damage, or injury resulting from use of the Website or Service.
- The Service is provided “as-is” without warranties of any kind, including fitness for a particular purpose.
- We do not guarantee specific outcomes or results from use of the Service.
eREC Privacy Policy
Effective Date: October 1, 2025
Last Updated: October 1, 2025
findeREC Inc. (“we,” “our,” “us”) respects your privacy and is committed to protecting your personal information. This Privacy Policy explains how we collect, use, and protect your data, including rights available to residents of California and the European Union/European Economic Area (EU/EEA).
1. Information We Collect
- Personal Information: Name, address, email, phone number, emergency contact details.
- Financial Information: Payment details (for Premium Membership).
- Demographic & Technical Information: Age, location, browsing activity, IP address, device details.
2. How We Use Information
- To provide, maintain, and improve the Service.
- To process transactions and manage Membership.
- To display authorized emergency contact information to other Users (with your consent).
- To communicate with you regarding account status, security, or updates.
- To comply with legal obligations and enforce our Terms of Service.
3. Sharing of Information
- With trusted service providers (payment processors, hosting, customer support, analytics).
- With law enforcement or regulators, if required by law.
- In the case of merger, acquisition, or transfer of ownership.
- We do not sell your personal information to third parties.
4. Security
- SSL encryption for data transmission.
- Financial data is securely processed by third-party providers and not stored on our servers.
- We use administrative, technical, and physical safeguards to protect your information.
5. Your Rights
Depending on your jurisdiction, you may have the right to:
- Access, correct, or delete your personal information.
- Restrict or object to processing of your data.
- Withdraw consent at any time.
- Receive a copy of your data in a portable format (data portability).
- Requests may be submitted to privacy@findeREC.com. We will respond in accordance with applicable law.
6. Data Retention
We retain information only as long as necessary for the purposes described, unless a longer retention is required by law (e.g., tax, accounting, or security obligations).
7. GDPR (EU/EEA) Compliance
If you are located in the European Union/European Economic Area, the following applies:
- Legal Basis for Processing: We process your personal data based on one or more of the following:
- Your consent (e.g., displaying emergency contacts).
- Contract necessity (e.g., fulfilling your Membership).
- Legal obligations (e.g., compliance with tax laws).
- Legitimate interests (e.g., improving security and services).
- Your Rights under GDPR:
- Right to be informed about how your data is used.
- Right of access to your data.
- Right to rectification (correction of inaccurate data).
- Right to erasure (“right to be forgotten”).
- Right to restrict processing.
- Right to data portability.
- Right to object to processing.
- Right not to be subject to automated decision-making without meaningful human input.
- International Transfers: If we transfer data outside the EU/EEA (e.g., to U.S. servers), we use appropriate safeguards such as Standard Contractual Clauses (SCCs).
- To exercise GDPR rights, contact us at privacy@findeREC.com.
8. CCPA/CPRA (California) Compliance
If you are a California resident, the California Consumer Privacy Act (CCPA) and the California Privacy Rights Act (CPRA) provide specific rights:
- Right to Know: You may request details about the personal data we collect, use, and disclose.
- Right to Delete: You may request deletion of personal data, subject to legal exceptions.
- Right to Opt-Out: You may opt-out of the sale or sharing of your personal information. (We do not sell personal data.)
- Right to Non-Discrimination: You will not be discriminated against for exercising your privacy rights.
- Sensitive Personal Information: We do not use sensitive categories (e.g., health data, precise geolocation) for profiling or targeted advertising.
- Requests can be submitted to privacy@findeREC.com or by mail to:
PO Box 196942, Atlanta, GA 30321
Verification may be required before fulfilling your request.
9. Children’s Privacy
Our Service is not directed to individuals under 18. We do not knowingly collect personal information from children. If we learn that a child under 18 has provided personal information, we will delete it promptly.
10. Changes to This Policy
We may update this Privacy Policy from time to time. If significant changes are made, we will provide notice by posting on the Website or emailing Members at least 30 days before the changes take effect.